When we talk about Identity and Access (IAM) what do we really mean? For me, it boils down to who you are and what you are entitled to access.
Simple statement, but it does start to get rather complicated when you think about Identity Management.
If you think about your own organisation what directory service does it use? Probably Active Directory Domain Services (AD DS). Think about how many years it has it been fine tuned with integration with third party solutions such as MFA, SSO and VPNs.
The list does truly go on and on. Most organisations will treat their on-premises Active Directory Domain Services (AD DS) as the one source of all truth for users, groups, permissions and passwords.
So the question is how does AWS deal with IAM?
What Is AWS IAM?
It is AWS hyperscale web service that allows users and services shared access to your AWS account. It uses an eventually consistent model, which in a nutshell means that changes are not immediately available.
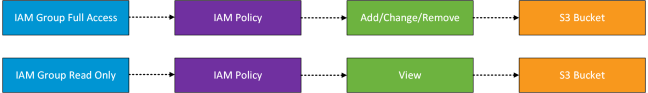
Users are authenticated and then authorised to use AWS services. To ease the management of individual users, groups are used. Policies are applied to groups which then dictate what the user or service can do.
Policies are JSON documents, used to define actions, effect, resources and conditions on what can be evoked for example:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "VisualEditor0",
"Effect": "Allow",
"Action": [
"s3:GetObject",
"s3:DeleteObject"
],
"Resource": "*",
"Condition": {
"IpAddress": {
"aws:SourceIp": "192.168.1.0/24"
}
}
}
]
}When you create an IAM user, they can’t access anything until you give them permission.
It should be noted that actions or resources which are not explicitly allowed are denied by default.
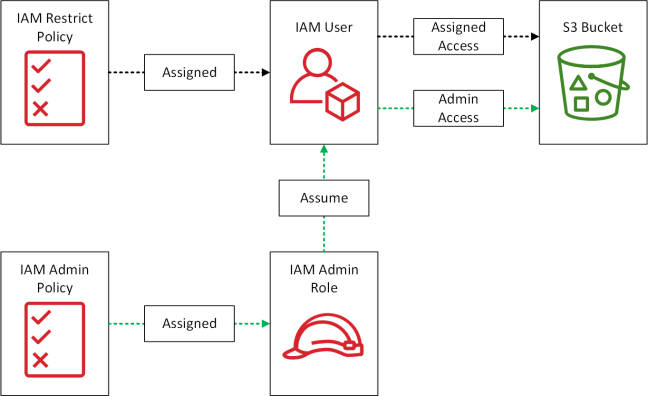
We also have IAM Roles, which are similar to users but are AWS identities with permissions (JSON policy) which determines what can or can’t do. It is important to note that IAM Roles don’t have any passwords or long terms access credentials. Access keys are created dynamically and provided on a temporary basis. Typically they are used to delegate access to applications or services.

IAM Roles can also be used to provide users with enhanced privileges on a temporary basis for example a user requires occasional admin access to an S3 bucket.
To enable policies to be tested before you apply them into production, AWS have a handy policy simulator which can be found here.
Identity Federation
AWS IAM supports identity federation for delegated access to either the AWS Management Console or APIs. Federated users are created within your corporate directory outside of the AWS account.
These can be web identity providers such as Amazon, FaceBook, Google or an OpenID Connect provider.
Within the enterprise world, we tend to see Active Directory Domain Services used in conjunction with Active Directory Federation Services. AWS have integration using Security Assertion Markup Language 2.0 (SAML 2.0) using STS AssumeRoleWith SAML.
A high level overview of this is shown below in the diagram below.
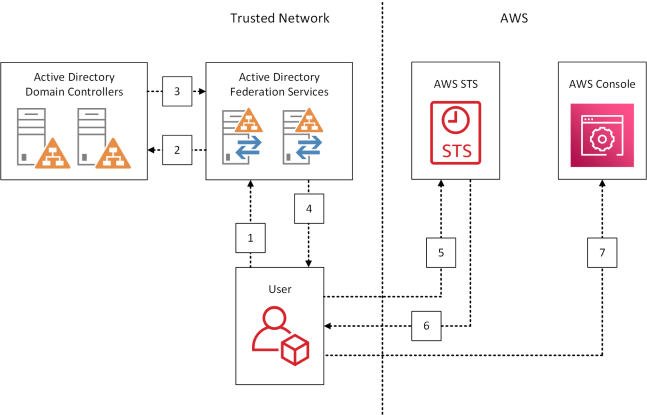
- User browsers to URL and is redirected to AD FS sign in page
- User enters Active Directory credentials
- User authenticated by Active Directory Domain Services
- Users browser receives a SAML 2.0 assertion
- User browser posts the SAML 2.0 assertion to AWS STS
- AssumeRoleWithSAML requests temporary security credentials and constructs a sign in URL for the AWS Management Console
- User browser receives the sign in URL and is redirected to the AWS Management Console
Single Sign On Cloud Applications
To provide easier integration with popular cloud applications
such as Dropbox, Office365 and SalesForce. AWS provide single sign on (SSO) using SAML 2.0via a configuration wizard.
Further information can be found here.
MultiFactor Authentication
AWS MFA provides an extra later of security to reduce the overall risk of compromised credentials. Providing a secondary authentication step for Management Console and API users.
For the MFA device, you have a choice of three items:
- Virtual MFA Device
- Hardware Key
- Hardware Device
This link shows which form factors can be used across devices.
Final Thoughts
AWS IAM is a web scale directory that can provides integration with on-premises directory services and cloud applications. Interestingly this is an added value service with no extra cost, which is a different approach from traditional licensing vendors.