Knowledge
- Describe characteristics of required Active Directory domain accounts (e.g., permissions).
- Describe characteristics of required Active Directory groups
- Identify and describe the GPO template files
- Describe Organizational Units (OUs) for machine accounts and kiosk mode client accounts
- Verify trust relationships
Active Directory Requirements
Each View Connection Server must belong to an Active Directory domain, in my case this is vmfocus.local. The View Connection Server must be a member server and not a domain controller (same requirements for vCenter Server).
Note, the View Connection Server can be located in a different domain as along as you have a two way trust relationship in place.
Active Directory Security Groups are used to specify which users are allowed to access which desktops and pools. Active Directory Security Groups are also used to define which users are allowed to administrator the View Connection Server. To make things simple, I have created two Security Groups:
- ViewAdministrators
- ViewUsers
Note, Security Servers reside in the DMZ and as such are not required to be part of an Active Directory domain.
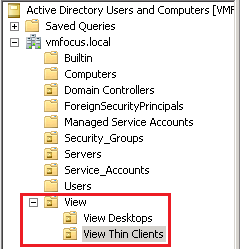
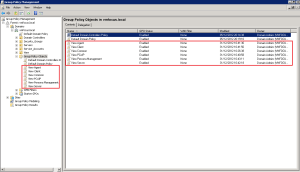
Organizational Unit’s should be created for View Desktops, to ensure that only specific Group Policy Objects are applied to them. As you can see I have created one called ‘View Desktops’.
Different OU’s should be used for Kiosk/Thin Clients as different Group Policy Objects will be applied to them e.g. for a kiosk/thin client you would want to be locked down so only View can be launched and on a normal laptop or desktop the Group Policy Object would be less restrictive.
Template Files
VMware View comes with a number of Administrative Templates twhich have common configuration settings to make our life a bit easier!
These can be found on your View Connection Server under …VMwareVMware ViewServerextrasGroupPolicyFiles
To import the ADM template files, launch Group Policy Management
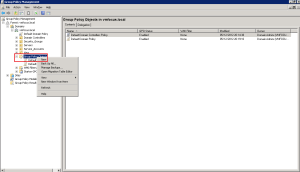
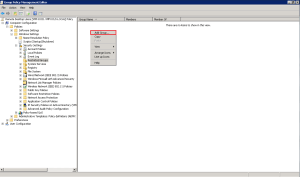
Right Click Group Policy Objects and click New
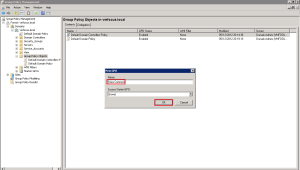
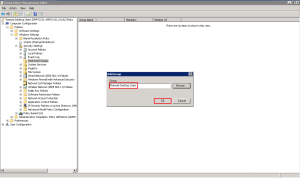
Give the new Group Policy Object a name, in my case, I’m going to roll with ‘View Common’ then hit OK
Now we are going to Right Click and Edit the ‘View Common’ Group Policy
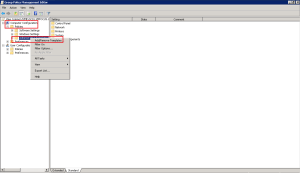
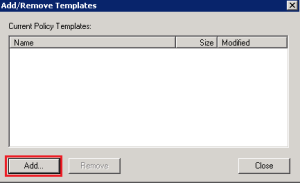
Double Click ‘Computer Configuration’ then expand ‘Policies’ and lastly Right Click Administrative Templates and select Add/Remove Template
Click Add
Browse to the location on your View Connection Server and select the ADM template you want to add. In this example, we are going to use vdm_common.adm by going to \VMF-CON01c$Program FilesVMwareVMware ViewServerextrasGroupPolicyFiles
If you have been successful, you should see the ‘vdm_common’ ADM in your Add/Remove Templates dialogue box.
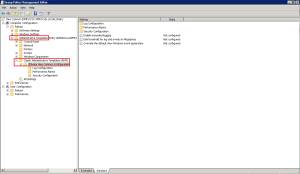
To verify the ‘vdm_common’ ADM expand Administrative Templates > Classic Administrative Templates (ADM) and you should see VMware View Common Configuration
Rinse and repeat for the rest of the View ADM templates you want to import.
TOP TIP: Create a GPO for each View ADM Template, to make management easier.
Remote Desktop Users
To allow users access to there View Desktop, we need to give them the Remote Desktop Users rights. Does this mean that each user has access to any desktop? Nope, as the connection still goes via the ‘View Connection Server’ which checks rights to access the relevant desktop.
The easiest and most effective way to grant ‘Remote Desktop User’ rights is to use Restrictive Groups.
Create a new Group Policy Object, I’m going to call mine ‘Remote Desktop Users’, I know very original!
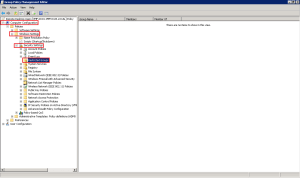
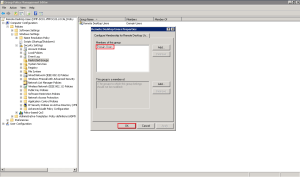
Edit the GPO, and browse to Computer Configuration > Windows Settings > Security Settings > Restricted Groups
Right Click anywhere on the right hand side and Select Add Group
Type in Remote Desktop Users and hit OK
Now we need to specify who is going to be a member of the Remote Desktop Users group. Click Add from the ‘Members of this group’ dialog box.
To keep things simple, I’m going to add ‘Domain Users’
Hit OK and you will see ‘Members of this group’ has been updated to include ‘Domain Users’.
Now you need to link the ‘Remote Desktop Users’ GPO to the appropriate OU in your Active Directory environment.








2 thoughts on “VMware View – Objective 1.5 Preparing Active Directory For Installation”