Knowledge
- Describe ThinPrint architecture
- Identify ThinPrint services
- Register .dll file
- Configure GPO
- Import location printing ADM file
Printing is the nemesis of the VDI world, how do we get that PDF from the View Desktop to the users client and enable everyone else to work? We are now entering into the promised land.
OK, I have a confession to make, I despise printers, they are the root of all evil and probably the biggest pain for Desktop Support Engineer. I don’t actually own a printer and to be honest, nor do I want to, so this particular objective is going to be theory based (well at least for me).
Now that I have that off my chest, I think we can carry on with Objective 2.9 Configure Remote and/or Location Based Printing For View Desktops
Describe ThinPrint Architecture
Before we talk this printing malarkey, it’s probably an idea to get an understanding of the steps taking to print inside a VDI environment.
In a traditional physical Desktop environment, the print flow is:
Physical Desktop User Prints > Desktop Print Spooler > Print Traffic Sent Across Network/USB > Print
The VDI environment follow the same principle, however the printer isn’t directly connected by LAN or USB.
View Desktop User Prints > Print Traffic Sent To Physical Windows Desktop > Physical Desktop Spooler > Print Traffic Sent Across Network/USB > Print
Now this isn’t so bad when working on the LAN, as the configuration we aren’t so worried about bandwidth, but when we are printing over a WAN, then we have some dramas!
VMware understood the challenges faced with printing inside the VDI environment and they licensed Thin Print under an OEM Agreement.
When you install the View Agent and the View Client, the ThinPrint drivers are automatically installed.
The print process works in the same way that I described above, however the print job is compressed and encrypted. The steps are:
- User prints inside View Desktop, the print job is captured by the ‘ThinPrint Generic Driver’ which is automatically installed as part of the View Agent into the View Desktop.
- The print job is compressed by the ‘ThinPrint Generic Driver’ and then sent over the WAN to the Windows Physical Desktop.
- The Physical Windows Desktop (which has View Client installed) then decompresses the print job and sends it too the print spooler.
- The Physical Windows Desktop then spools the print job to the printer.
Print Drivers
I wanted to take a slight detour and talk about Printer Drivers. The Print Driver needs to be available for the print job to happen, this can be achieved in a few ways.
Physical Windows Desktop this option can work if you are reusing old Windows Desktops to be your ‘dumb terminals’ . Just install the Print Drivers on the physical desktop.
Thin Client this causes us an issue as we cannot install any Print Drivers, as we have no host Operating System. In this case we need to install the Print Drivers into the View Desktop. If you have a Desktop Pool that is used company wide which has 50 printers, you don’t really want to ‘bloat’ your Linked Clone Image with all the drivers. Instead you probably want to install Print Drivers on demand, which is something I will refer to later in this blog post.
Identify ThinPrint Services
We have two services which are installed on the View Desktop which are:
- TP AutoConnect Service
- TP VC Gateway Service
The TP AutoConnect Service creates the printers in the users View Desktop
The TP VC Gateway Service is the grafter, it grabs the print data from the applications to enable it to be encrypted and compressed.
On the View Client (Physical Windows ) Desktop we don’t have any services installed, as it’s within the View Client, however we do have a registry key that we can alter to enable or disable ThinPrint.
Enabled HKEY_LOCAL_MACHINESOFTWAREWow6432NodeThinPrintClient Default State 0
Disabled HKEY_LOCAL_MACHINESOFTWAREWow6432NodeThinPrintClient Default State 1
Register .dll File
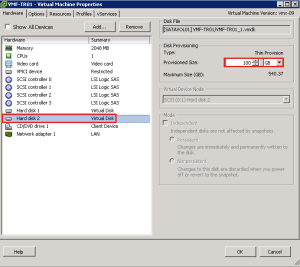
To allow us to access the Group Policy settings for ThinPrint we need to register a .dll on an Active Directory Domain Controller.
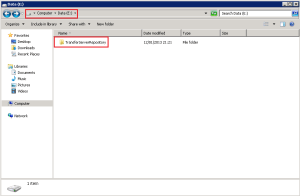
The .dll is called TPVMGPoACmap.dll and is located on your Connection Server under C:Program FilesVMwareVMware ViewServerextrasGroupPolicyFilesThinPrintx64
Copy this .dll to the root of your Domain Controller.
Jump into the CMD and type regsvr 32 C:TPVMGPoACmap.dll
Boom, we have success!
Configure GPO
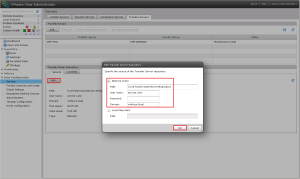
This is really straight forward, first of all we need to create a Group Policy, I’m rolling with a GPO called ‘Location Based Printing’ and I have linked it to the Organisational Unit ‘View Desktops’
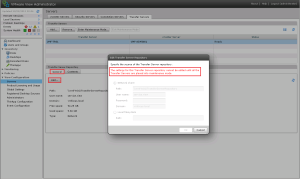
Naturally, the GPO is blank at the moment. Let’s edit it and go to Computer Configuration > Policies > Software Settings and you will see AutoConnect Map Additional Printers for VMware View
Double Click AutoConnect Map Additional Printers for VMware View and set the Policy to Enabled by Clicking in the Top Right Hand Corner
Import Location Printing ADM File
We have really imported the location ADM file by performing the above, I wanted to give you an overview of the Location Printing settings.
Click Add in the top left and you will see some columns appear ‘as if by printer magic’.
We can define who can access the printer by:
- IP Range
- Client Name
- MAC Address
- User/Group
In most environments it’s probably going to be via IP Range or User/Group
The Printer Name column, is the name we want the printer to appear as in the View Desktop.
The Printer Driver column, is really important, this is the driver which is installed on the Physical Desktop. Ensure that you type this in exactly as it appears on the Physical Desktop.
If the printer is locally attached then you don’t need to enter any details in under the IP Port/ThinPrint Port. If you are using a network printer then you need to enter it in the format IP_x.x.x.x e.g. IP_192.168.1.10
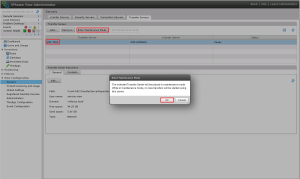
As you can see I have entered the details in for my Microsoft OneNote driver into AutoConnect Map Additional Printers
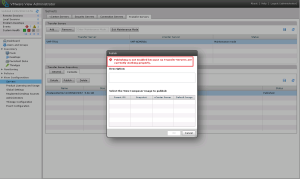
If we now check the ThinPrint Group Policy out you will see we have Extra Registry Settings Configured.