Knowledge
- Identify View Connection Server backup settings
- Identify View Global Settings
- Identify the account to connect to vCenter
- Add View license settings
- Modify Global Policies
- Configure external URL settings
- Identify View Connection Server general settings
- Identify default roles, custom roles, and what permissions are available
- Describe the use of folders within the View Connection Server
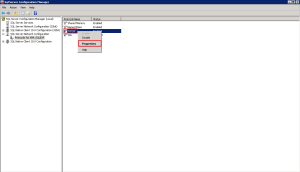
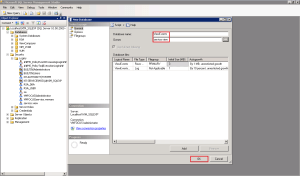
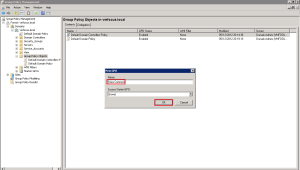
Identify View Connection Server Backup Settings
View Connection Backup Settings are located in View Configuration > Servers > Connection Servers you can perform a Backup Manually by Clicking on Backup Now
By default the Connection Server settings are backed up to C:Program DataVMwareVDMBackups on a daily basis at midnight. The default setting is to keep 10 backups.
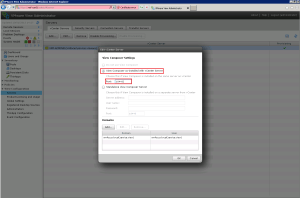
This information can be viewed by Selecting the Connection Server and Clicking on Edit and Selecting the Backup Tab
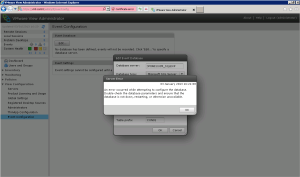
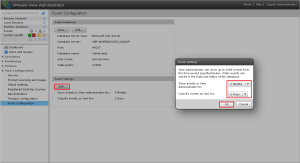
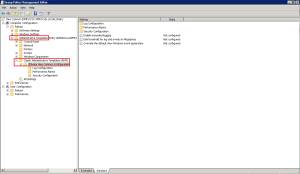
Identify View Global Settings/Modify Global Settings
View Global Setting allow the configuration of items such as Session Timeouts, Pre Login Messages and allows us to change the Data Recovery Password.
View Global Settings can be found at View Configuration > Global Settings
View Global Settings can be modified by Clicking on Edit to change either the General or Security Settings
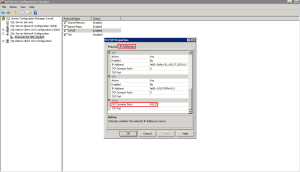
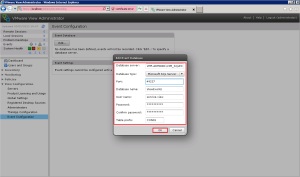
Identify The Account To Connect To vCenter
This is the account that forms the ‘link’ between View Connection Server and vCenter.
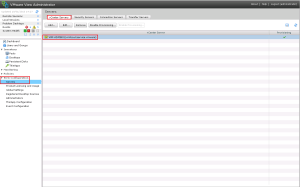
The account can be found by going to View Configuration > Servers > vCenter Servers
Add View License Settings
To Add your View Licenses go to View Configuration > Product Licensing & Usage > Edit License
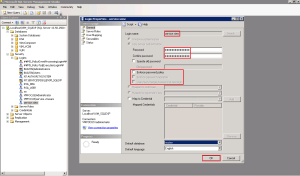
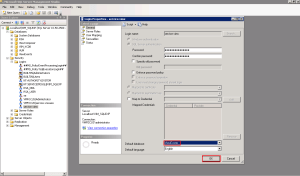
Configure External URL Settings
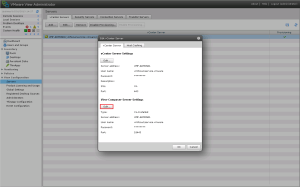
When you configure the View Connection Server, the External URL is going to be the internal FQDN of the View Connection Server.
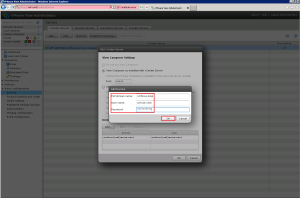
We want to change this to be an External URL, but which can resolved by internal clients. To achieve this we need to go to View Configuration > Servers > Connection Servers > Edit > General and change the External URL.
Old URL: https://vmf-con01.vmfocus.local:443
New URL: https://view.vmfocus.com:443
As we have changed the DNS name to something external it won’t be able to resolve it in DNS on the LAN. So let’s create an Active Directory Forward Lookup Zone for vmfocus.com and add in the A record view.vmfocus.com
Jump onto your Domain Controller and open DNS
Expand Forward Lookup Zones and then Right Click New Zone
Click Next
We want to create a Primary Zone so Click Next
The Primary Zone wants to be replicated ‘To all DNS servers running on domain controllers in this domain: vmfocus.local’
We are going to name the zone ‘vmfocus.com’ and Click Next
‘Allow only secure dynamic update’s and Click Next
Hit Finish and the vmfocus.com Forward Lookup Zone will be created
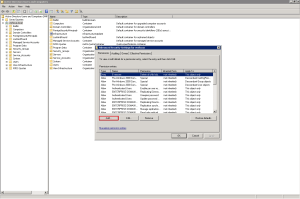
Go into the Forward Lookup Zone for vmfocus.com and a New Host (A or AAA)
Enter the first part of your external DNS name, for me it’s ‘view’ and then the internal IP address of your View Connection Server. Then Click Add Host
Now go to ping your external DNS name and it should be resolving correctly.
Identify View Connection Server General Settings
I’m slightly ‘miffed’ by this one, I don’t really understand what VMware want. I have searched through the Administration Security and Install guides and I can’t see anything relevant. So onto the next part.
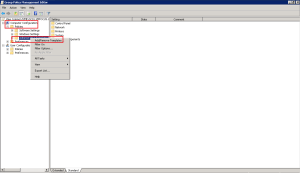
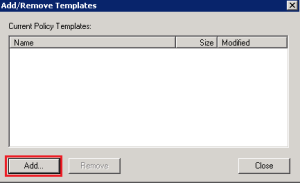
Identify Default Roles, Custom Roles, and What Permissions Are Available
Roles and Permissions enable the administrator to see items and also perform action on objects. If an administrator doesn’t have rights to view a certain item/area then this will not be visible.
As with vCenter, permissions can either be object specific or global.
View’s default roles are located within View Configuration > Administrators > Roles
The Default Roles are:
- Administrator
- Administrator (Read Only)
- Agent Registration Administrators
- Global Configuration and Policy Administrator
- Global Configuration and Policy Administrator (Read Only)
- Inventory Administrator
- Inventory Administrator (Read Only)
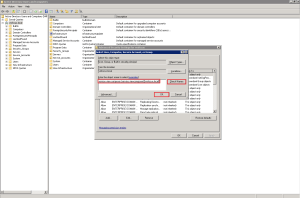
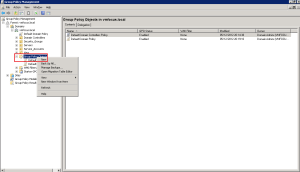
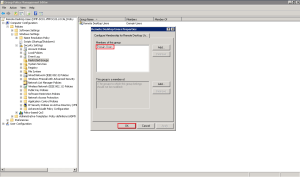
Custom Roles can be created by Clicking ‘Add Role’ As you can see View has a plethora of privileges.
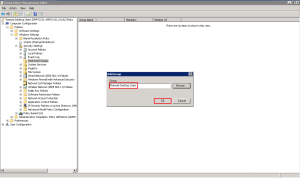
Then giving the role a name for instance ‘View Help Desk’ and choosing what permissions they have e.g. ‘Manage Desktops’
The Custom Role will then appear in the left hand side. Don’t forget you need to apply the Permissions to the Custom Role, otherwise it err won’t work!
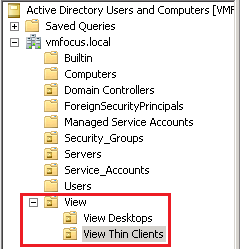
Permissions are essentially who we apply the Custom Role privileges too. Pretty much it’s going to be an Active Directory Security Group.
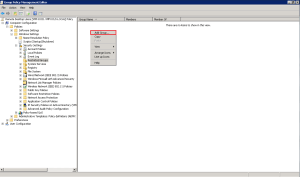
Select your Custom Role > Permissions > Add Permissions
Click Add and then Select what Security Group you are going to apply the Permissions too. I’m going to roll with ViewAdministrators
View’s Permissions are based around Folders, so we need to choose which Folder (or Root) that we want the Permissions to be applied too. These ViewAdministrators are new, so they can only have access to the ‘Manual Pool’
Quick recap, we have created a Custom Role called ‘View_Help_Desk’ who have Permissions to ‘Manage Desktops’. The users who can apply the Permissions to the ‘Manual Folder’ belong to the ‘ViewAdministrator’ Active Directory Security Group.
Describe The Use Of Folders Within The View Connection Server
Folders are at the epicenter of View permissions. As we assign Permissions too Folders, they should be designed in a logical format.
For example you may wish to have Folders that represent different Company Departments that have different View Desktops. These View Desktops are then managed by different View Administrators.
Accounts Folder > Managed By > View Help Desk Team A
Marketing Folder > Managed By > View Help Desk Team B
Sales Folder > Managed By > View Help Desk Team C
The only time Folders don’t come into play is when you have a Global Privilege such as ‘Manage Global Configuration and Policies’.